Project Managers
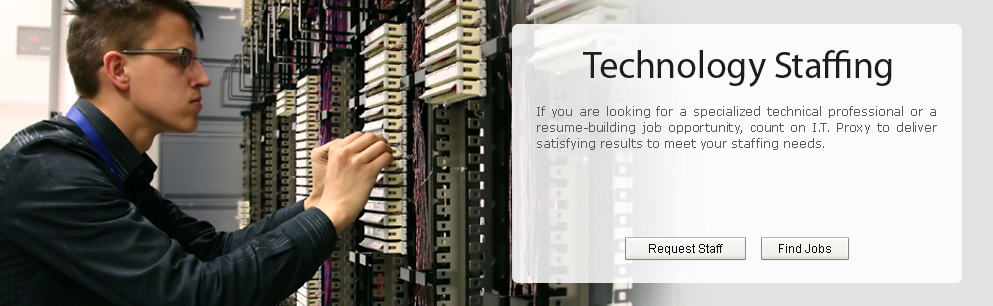
IT Proxy, a division of Proxy Personnel, provides professional IT staff for corporations, start-ups, and nonprofit organizations. Our experienced IT recruiters are fully equipped to staff positions requiring advanced mixtures of technology and are well versed in new technologies, recruiting trends, programming languages, and hardware. We combine world class project methodology with our subject matter experts to deliver solutions to some of the industry’s most complex IT challenges. Our employees have project management expertise in all of the following areas:
- Cloud Computing
- Virtual Networks
- Data Warehouse & Business Intelligence
- Application Integration and Customization
- Health Informatics
- Electronic Medical Records
- Anti – Fraud Technology (Banking)
CLOUD COMPUTING
Cloud computing is the delivery of computing as a service rather than a product, whereby shared resources, software, and information are provided to computers and other devices as a utility over a network (e.g. internet). Cloud computing provides computation, software, data access, and storage services that do not require end-user knowledge of the physical location and configuration of the system that delivers the services.
VIRTUAL NETWORKS
A virtual network is a computer network that consists, at least in part, of virtual network links. A virtual network link is a link that does not consist of a physical (wired or wireless) connection between two computing devices but is implemented using methods of network virtualization. The two most common forms of virtual networks are protocol-based virtual networks (such as VLANs, VPNs, and VPLSs) and virtual networks that are based on virtual devices (such as the networks connecting virtual machines inside a hypervisor).
DATA WAREHOUSE & BUSINESS INTELLIGENCE
A data warehouse (DW) is a database used for reporting and analysis. The data stored in the warehouse is uploaded from the operational systems. The data may pass through an operational data store for additional operations before it is used in the DW for reporting. A data warehouse maintains its functions in three layers: staging, integration, and access.
Business intelligence (BI) mainly refers to computer-based techniques used in identifying, extracting, and analyzing business data, such as sales revenue by products and/or departments, or by associated costs and incomes.
BI technologies provide historical, current and predictive views of business operations. Common functions of business intelligence technologies are reporting, online analytical processing, analytics, data mining, process mining, complex event processing, business performance management, benchmarking, text mining and predictive analytics.
APPLICATION INTEGRATION AND CUSTOMIZATION
Installation of software products that requires additional customization or development to ensure the systems meet the organizational requirements. This especially applies if the requirements are not “cookie cutter”, or are not available “out of the box”.
HEALTH INFORMATICS
Health Informatics is a discipline at the intersection of information science, computer science, and health care. It deals with the resources, devices, and methods required to optimize the acquisition, storage, retrieval, and use of information in health and biomedicine. Health informatics tools include not only computers but also clinical guidelines, formal medical terminologies, and information and communication systems. It is applied to the areas of nursing, clinical care, dentistry, pharmacy, public health, occupational therapy, and (bio)medical research.
ELECTRONIC MEDICAL RECORDS
Electronic Medical Records is an evolving concept defined as a systematic collection of electronic health information about individual patients or populations. It is a record in digital format that is capable of being shared across different health care settings, by being embedded in network-connected enterprise-wide information systems. Such records may include a whole range of data in comprehensive or summary form, including demographics, medical history, medication and allergies, immunization status, laboratory test results, radiology images, vital signs, personal stats like age and weight, and billing information.
ANTI-FRAUD TECHNOLOGY
Anti-Fraud Technology is enhanced technology that layer in protection through identification of suspicious transactions, computer and behavioral authentication and anti-phishing capabilities. The anti-phishing technology prevents cyber criminals from compromising agent computers and stealing customer information. The solution provides user and computer authentication technologies to prevent fraud from the point of login through completion of the transaction. The technology also conducts behavioural monitoring – flagging transactions for review if a customer suddenly changes his/her pattern during transactions.